Piergiorgio Venuti
Piergiorgio Venuti
New Acronis Cloud Backup model for end users and new reseller plan
New Acronis Cloud Backup model for end users and new reseller plan
Our Acronis Cloud Backup service is renewed with two distinct subscription types for end users and retailers / system integrators. With the former, it is possible to meet the needs of small and medium businesses that need to have a professional solution for managing their local and remote backups (Cloud). The second one, on the other hand, is able to meet the most complex requirements of System Integrators who will be able to use the service to implement ad-hoc Data Protection projects for their clients.
Starter
The Starter package protects a Workstation and three mobile devices by providing 30Gb of space on our Cloud. This solution is ideal for professionals or small studios where you want to safeguard data from a workstation and up to 3 mobile devices inside the office.
Basic
The Basic package protects five Workstations, one Server, three virtual machines, and fifteen mobile devices by providing 300Gb of space on our Cloud. This solution is ideal for professional or small businesses.
Professional
The Professional package protects an unlimited number of Workstations, Servers, Virtual Machines, and Mobile Devices by providing 2Tb of space on our Cloud. This solution is ideal for medium to large businesses.
The software agents of all Acronis Cloud solutions can also be used for local backups (local NASs) at no extra cost thanks to multiple backup plans that can be assigned to each system to be protected.
Acronis Cloud Backup Prices
- Acronis Cloud Backup - Starter
For small business
- 4.75/Month
- Workstation = 1
- Server = 0
- Virtual Machine = 0
- Mobile device = 3
- Storage space = 30 Gb
- Sign Up
- Acronis Cloud Backup - Basic
For medium business
- 63.41/Month
- Workstation = 5
- Server = 1
- Virtual Machine = 3
- Mobile device = 15
- Storage space = 300 Gb
- Sign Up
- Acronis Cloud Backup - Professional
For big business
- 253.69/Month
- Workstation = Unlimited
- Server = Unlimited
- Virtual Machine = Unlimited
- Mobile device = Unlimited
- Storage space = 2 Tb
- Sign Up
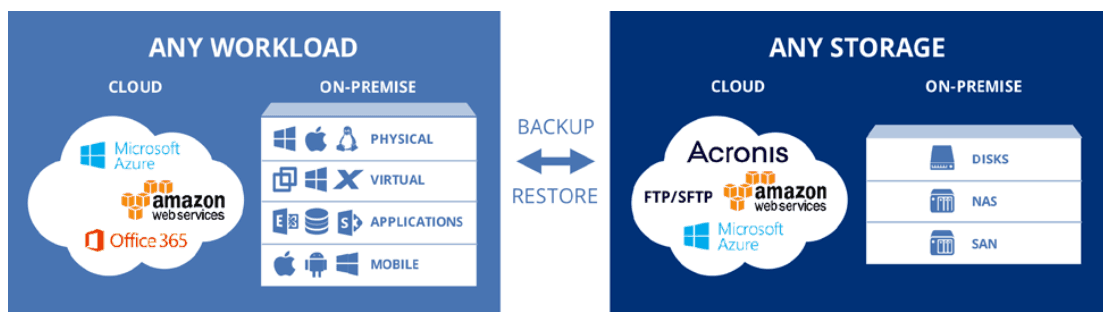
PROTECT ANY WORKLOAD, BACKUP TO ANY STORAGE
You, as a system integrator, need to support an increasing number of use cases to retain customers and expand your Total Addressable Market (TAM). Acronis Cloud Backup provides you with tools and options to protect any device in any location by backing up to any storage and recovering to any platform.
USEFUL LINKS:
A Hybrid Cloud Solution for System Integrator and reseller
[btnsx id=”2931″]
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
© 2024 Cyberfero s.r.l. All Rights Reserved. Sede Legale: via Statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Cod. fiscale e P.IVA 03058120357 – R.E.A. 356650 Informativa Privacy - Certificazioni ISO