Log Management
 Piergiorgio Venuti
Piergiorgio Venuti
Log File Management with the Secure Online Desktop service
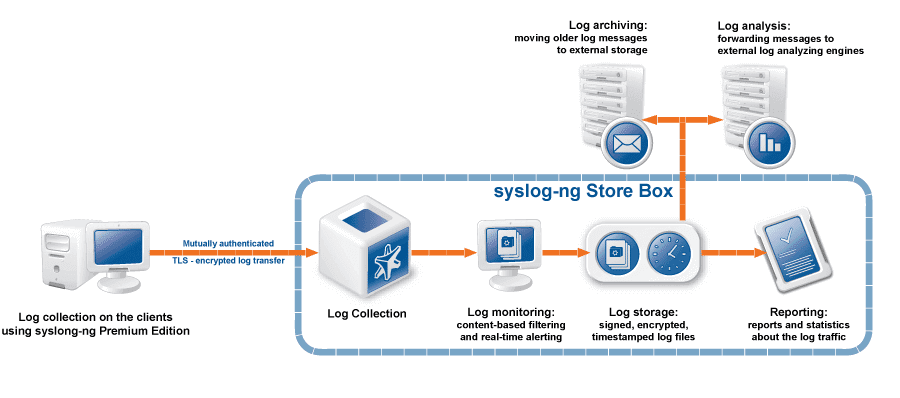
IT systems produce large quantities of log files, very useful tools for guaranteeing data security and application stability. However, in a complex ecosystem, the quantity of files and their location can become two insurmountable obstacles to overcome, in case it is necessary to consult the data efficiently. This is where log management systems come into play, which thanks to technologies…
 Piergiorgio Venuti
Piergiorgio Venuti
New service | Log Management – High performance service for collecting logs
syslog server – High performance service for collecting logs Use all the strengths of the syslog-ng Premium Edition Find logs, secure sensitive data with granular access policies and generate reports Forward logs to third-party tools SYSLOG SERVER – CLOUD LOG MANAGEMENT SERVICE TO MANAGE YOUR LOGS Log Management service allows you to keep logs (applications, system, audit logs, query…
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2024 Cyberfero s.r.l. All Rights Reserved. Sede Legale: via Statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Cod. fiscale e P.IVA 03058120357 – R.E.A. 356650 Informativa Privacy - Certificazioni ISO



















