Piergiorgio Venuti
Piergiorgio Venuti
Introducing a set of new GDPR tools
GDPR tools
GDPR, the European Union regulation aimed at strengthening and unifying data protection for all individuals within the European Union comes into force on 25th May. The regulation brings a huge change to European data security, but it also impacts many non-EU based business as well. If you’d like to find out more about GDPR you can read our previous blog post.
We have introduced numerous changes within our portal to ensure that data protection complies with the GDPR
GDPR tools
Get consent with GDPR-friendly forms
The GDPR sets a high standard for consent for gathering and processing personal data. Consent requires a positive opt-in, which means you can’t use pre-ticked boxes or any other method of default consent. Explicit consent requires a very clear and specific statement of consent and the consent requests must be separate from other terms and conditions.
In addition to what we did for the order we add explicit check box in our registration form as well.
Highest professional standards of data handling.
Secure Online Desktop now offers a set of features that are aimed at providing your customers with the best standards for data processing.
♦ Data retention
◊ Automatically remove empty client profiles after 6 months since sign-up. [bg_collapse view=”button-blue” color=”#ffffff” expand_text=”Show More” collapse_text=”Show Less” ]Client profiles that does not have any of the following:
1) Paid invoices
2) Active hosting account
3) Registration domain
4) Unclosed support ticket[/bg_collapse]
◊ Automatically remove inactive client profiles after 120 months since last payment. [bg_collapse view=”button-blue” color=”#ffffff” expand_text=”Show More” collapse_text=”Show Less” ]Client profile the does have paid invoices on file, but does not have any active account/domain or unclosed support tickets.[/bg_collapse]
♦ Deletion Handling: When client request deletion his account status will be changed to Pending removal, it will be removed after Deletion delay period.
♦ Deletion Delay: Permanently remove client data after 30 days (since last login)
♦ Export / report settings:
◊ Contacts
◊ Accounts / Services
◊ Domains
◊ Change log
◊ Transactions
◊ Invoices
◊ Tickets
The right to be informed
Under GDPR individuals have the right to be given information about how their data is being processed and why. We created multiple policy links (for separate terms) that client needs to accept in client portal, by ticking the relevant checkbox. Agreeing on the given terms will be required for the customer to proceed to checkout.
The right to access
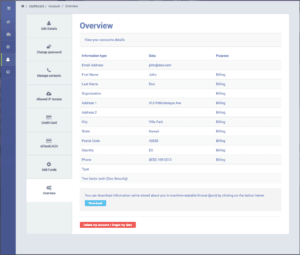
Individuals have the right to obtain the confirmation as to whether or not personal data concerning them is being processed, where and for what purpose. In the client portal each registered client has access to the overview of their personal information. Under My Account→ Overview client can view their details along with the purpose for each data that is being collected (billing or non-billing; defines whether or not the data is needed for invoicing and hence it may be required to keep that data for a given period of time).
Secure Online Desktop admin area also provides you with the possibility to generate PDF report with client data, the json file contains other information (such as c
The right to be forgotten
GDPR gives individuals the right to have their personal data erased. With Secure Online Desktop, clients can request to have their account deleted and their data forgotten with just one mouse click. We’ve made sure that the client will be able to start the account removal process only if there are no unpaid invoiced linked to their account and there are no active services that can’t be cancelled. Requesting the account to be deleted will assign the account with the ‘pending removal’ status and deleted after certain period of time (30 days).
If a client requests for their data to be forgotten but are required to keep their data for a given period of time (for legal or tax purposes etc). we have the possibility to remove as much client information as possible, without removing the data required for billing/contract purposes. Secure Online Desktop’s client anonymization feature allows us to close client profile, terminate client services, clear client changes log, emails and tickets and remove ALL non-billing data.
The right to object
Individuals have to right to object at any time to processing of personal data concerning them. With Secure Online Desktop our clients can review all of the terms and services they have given their consent to and withdraw that consent at any time. All changes made to client profile are logged, so if needed we can prove that the customer has given us the consent to gather/process their data (and when) and if the customer withdraws the consent we can determine when it happened.
Secure Online Desktop Newsletter module for email and e-commerce marketing also provides quick and easy ‘unsubscribe’ option in each email send to the customer.
The right to data portability
As per GDPR individuals have the right to receive a copy of the personal data, free of charge, in an electronic format. Secure Online Desktop enables to easily downloaded to the json file all personal information gathered in client profile with the single click of the mouse from My Account→ Overview section in client area.
[btnsx id=”2931″]
Useful links:
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2024 Cyberfero s.r.l. All Rights Reserved. Sede Legale: via Statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Cod. fiscale e P.IVA 03058120357 – R.E.A. 356650 Informativa Privacy - Certificazioni ISO